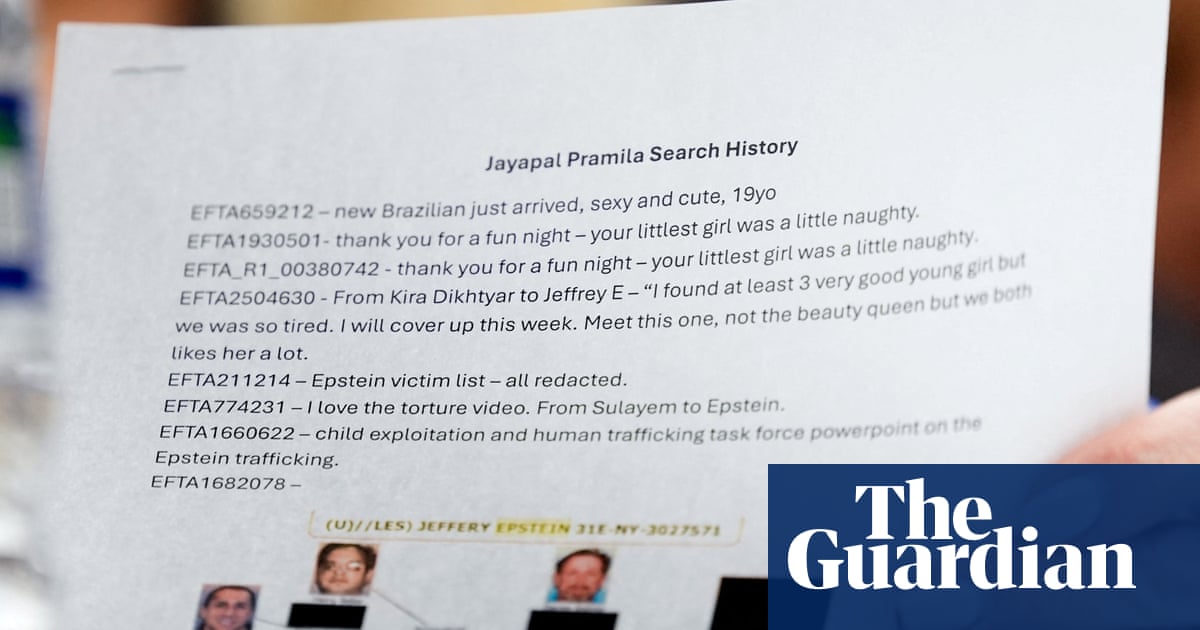
Photographs taken by Reuters during a congressional hearing on Wednesday showed the US attorney general, Pam Bondi, holding a document titled “Jayapal Pramila Search History”, listing files that the Democratic US representative Pramila Jayapal had accessed during her review of the Epstein materials.
“DoJ has extended Congress the opportunity to review unredacted documents in the Epstein files,” a justice department spokesperson said in a statement. “As part of that review, DoJ logs all searches made on its systems to protect against the release of victim information.”
“There is someone or two people from the [justice department] monitoring you as you sit on those computers,” Mace told NPR. “There is a tech person who logs you into the computer. They log you into the computer because they’re giving you your own identification. They are tracking all of the documents that members of Congress open, and they’re tracking everything that you do in that room.”
I think it would be really big news if they suddenly stopped trying to play dirty.


I think you may be misunderstanding me. There are actual infosec protocols and standards involved, well-defined best practices, not just guesses.
Third party use of user credentials invalidates the entire tracking process, as does allowing/mandating visual observation of the resources accessed.
In both events, the resources are not actually being accessed by the person tracked. So while you talk about creating a user account for each lawmaker (standard) and creating a report of their resource usage (standard), in reality information security has already been breached three times. First, by not giving the credentials to the user and making the user responsible for seeing to their privacy. Secondly, by the third party that typed in the credentials for the user. Thirdly, by the observing party who visually accessed the resources in tandem with the user.
That’s not standard at all, it’s complete shit. And worse still, it killed the legitimacy of any real auditing.
I’ll explain. Let’s say I’m Raskin, and I jumped through these hoops to see these files. Okay, fine, I saw them and went home. But now it’s next week, and suddenly I am being accused of selling information I saw in the files to a media outlet, except I never saw these other files. They weren’t in the set I personally looked at.
Pull your auditing and tell me how far it gets you now. You won’t have any idea who really pulled those extra files, or even if they were pulled at all.
That’s why it’s not even basic information security.
EDITED TO ADD: that’s not even a software generated report. Looking at the actual picture of Pramila Jayapal’s EFTA searches, it is a hand typed list with descriptors and even an EFTA number typo. The fifth item, the list of Epstein’s victims, is EFTA211240, not EFTA211214.